
There are two types of people: those who use the same password for all their accounts; and those who use a password manager. Ok this may not be entirely true, but fact is that it is impossible to memorize a safe and different password for all logins you have. With a password manager you don't have to even know your passwords anymore, except for one: the master password.
In the cloud?
There are many different password managers. Most of them, like for example 1Password or Lastpass, provide an online service where all passwords are stored safely (you hope!) in "the cloud". That's convenient because you have access to them everywhere, but it also means that all your very sensitive and important data is in the hands of a private party, of which you only can assume and hope that they guard and protect it well.
Offline?
If you worry about that, or if you simply are too cheap to pay for a service (most services are not free) you could opt for an offline password manager, like Keepass. That is, simply said, an encrypted safe in a file on your own device. You can be sure no one except yourself has access (unless you do something stupid). That may be safer, but has the disadvantage that you have to set something up to synchronize that file between all your devices. For that you can use a service like Dropbox, or if you prefer a self hosted solution: Nextcloud.
Sync conflicts!
Most of the time this works fine. But, sooner or later, you will encounter sync conflicts. That happens for example when the file has been modified on more than one device, but synchronization was delayed, for whatever reason. As the safe is a binary file that cannot be merged automatically, suddenly you end up with two different versions of your safe. Merging them manually can be a major PITA. So often the only viable option is to delete one of them, possibly causing the loss of passwords.
Online, distributed, and self hosted?
I have used Keepass for a long time this way but conflicts kept happening from time to time, so I started looking for a better alternative. Couldn't there be a solution that was self hosted, open source, and distributed, with better conflict resolution?
As a matter of fact, there is. pass, "the Standard Unix Password Manager". Basically, it is not much more than a few convenience scripts around gnupg en git. Every password is in a different file, encrypted by gnupg. And all files are in a git repository. Git can be used fully decentralized, and is designed to sync data between many machines, and it has excellent conflict management capabilities. And of course it offers logging, history and undo capabilities.
Installation and setup
Let's start with the bad parts: installation is not trivial. Some knowledge and experience is needed and things are less "user friendly" than other password managers. For example you need to take care of your gnupg key pair for encryption and decription, and of course it really helps if you know your way around git. If you want to use it in a decentralized way, you also need a secure server to host the git repository, which needs to be accessible using ssh.
I am unable to cover detailed installation instructions here, instead I would like to refer to this HowTo, the official website and the man page.
Pass in practice
Some examples. Let's make a new password for example.org. It's easy on the command line: pass generate sites/example.org.
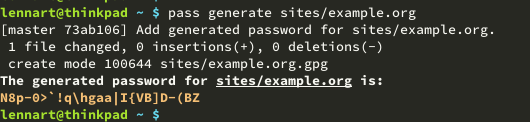
Now the password has been encrypted and saved in the file sites/example.org.gpg and it can be decrypted using pass sites/example.org. The file is only available local though, to make it available to others / other devices, push the changes with pass git push.
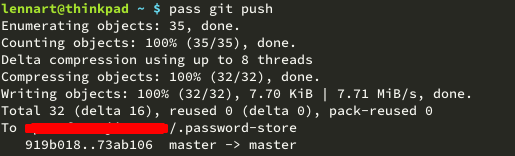
To pull changes from upstream, you probably guessed it, just use pass git pull.
As the password store is a normal git repo, you could also do all available git operations directly on the repo itself, which by default can be found at ~/.password-store. That means you could do git move, git rm or things like git log etc. Of course any git GUI can be used as well.
Put it on github or host it yourself
In theory you could put your password repository in a private repo at github. But that defeats the purpose, we were trying to cut out all third parties. In addition, this could be less safe. Although all file contents are encrypted, the file names itself are not, which could be sensitive metadata. So it might be best to host your repository safely on your own server. I use a VPS for this, accessible using ssh.
Clients and plugins
Besides the command line client, there are apps available for Android and iOS, as well as plugins for Firefox and Chrome. For pass itself there are useful plugins available like OTP plugin for generation of time based one time passwords, and there are import tools for LastPass, Keepass and many others.
For nerds only
By now you probably realized that pass is not the easiest solution around. It requires considerable skills and it takes some fiddling to set up properly. Configuration and usage is less intuitive slick than other commercial in the cloud solutions. You will need some proficiency with tools like gnupg, git and ssh, and you need your own ssh accessable server for hosting the repo. And doing everything yourself means that you are fully responsible for all security as well. That makes pass unsuitable for people like your grandma.
But if you're a tech savvy (and maybe a bit paranoid) linux nerd, you won't be discouraged by this, and pass can be an excellent and very useful tool.



